Cybersecurity is no longer just a concern for large enterprises; it has become a necessity for developers, startups, and even individual users. As the number of computer threats grows with hacking of information and ransomware attacks as well as phishing schemes, it is necessary to have appropriate security software to ensure the safety of sensitive data as well as integrity of the system.
Among the most favorable aspects of cybersecurity beginners, you do not always have to use costly software. Open source cybersecurity solutions provide the ability to analyze networks, identify vulnerabilities and improve the defenses at no cost, as the tools are very powerful. These tools are commonly relied upon by professionals the world over by way of penetration testing frameworks, intrusion detection systems and so on.
In this article, we will discuss the 15 most popular Open Source Cybersecurity Tools that can assist you in securing systems and determining risks and enhancing your overall security posture regardless of whether you are an amateur or a veteran security professional.
Why Choose Open Source Cybersecurity Platforms?
- Affordable without losing functions: Open sources are free and so they suit start-ups, students and small businesses that lack the financial means to buy security solutions that are very costly yet they require a good security.
- Transparency and trust: The publicly accessible source code will allow the security experts to inspect, test, and enhance the software to lower the chances of concealed vulnerabilities or backdoor.
- Very customizable and flexible: The tools are customizable by the users depending on their requirements and this may be in the form of adding new features, automation, or synchronization with systems that are already in place.
- Strong community support: There are active communities supporting popular open source tools to provide regular updates, plugins, and documentation, which means that they are continuously being improved.
- Extensive usage among the professionals: Open source tools are being applied by many cybersecurity specialists and organizations in the real world as their reliability and effectiveness has been proven.
Key Features To Look For In Cybersecurity Tools
- Extensive threat detection features: A quality tool must be capable of identifying various categories of threats like malware, vulnerability, unauthorized access, and suspicious activity in the network.
- User-friendliness and the learning curve: Intuitive interface or well documented tools can enable a user to learn how to use them easily and how to use them at the outset of use particularly when the user is new.
- Routine upgrades and maintenance: There are very high chances of cyber threats changing fast, which is why it is prudent to adopt tools that are regularly updated with the newest threat intelligence and patches.
- Interconnection with other systems and tools: It can be integrated with SIEM systems, logging tools, or cloud Security platforms, which improve the general monitoring and response to security.
- Different environment scalability: The tool must be capable of managing large workloads and system sizes whether on a personal scale or on an enterprise scale.
List Of 15 Best Open Source Cybersecurity Tools
1. Wireshark
Website:https://www.wireshark.org/
Wireshark is one of the most widely used network protocol analyzers in the world. It allows security professionals to capture and interactively browse network traffic in real-time. Whether you’re troubleshooting network issues or investigating suspicious activity, Wireshark provides deep visibility into packet-level data, making it a must-have tool for analysts.
The tool supports hundreds of protocols and provides detailed insights with a powerful filtering system. As one of the Open Source Cybersecurity Tools, it is especially useful for detecting anomalies, analyzing malware traffic, and understanding how data flows across networks. With its intuitive GUI and strong community support, Wireshark is suitable for both beginners and advanced users.
Top Features:
- Real-time packet capture and offline analysis
- Deep inspection of hundreds of protocols
- Powerful display filters for precise analysis
- Cross-platform support (Windows, Linux, macOS)
- Rich visualization with color-coded packets
2. Nmap
Website:https://nmap.org/
An effective open-source program for network discovery and security auditing is called Nmap (Network Mapper). Through packet transmission and response analysis, it assists in identifying hosts and services on a network, making it one of the most reliable open source cybersecurity platforms. This makes it essential for penetration testers and system administrators looking to assess network exposure.
Beyond basic scanning, Nmap can detect operating systems, versions of running services, and even vulnerabilities. Its scripting engine (NSE) allows users to automate complex security tasks, making it highly flexible. Nmap is widely trusted for mapping networks and identifying potential attack surfaces.
Top Features:
- Network discovery and port scanning
- OS and service version detection
- Nmap Scripting Engine (NSE) for automation
- Flexible output formats (XML, text, etc.)
- Supports large-scale network scanning
3. Metasploit Framework
Website:https://www.metasploit.com/
Metasploit Framework is a leading open-source penetration testing platform used for developing, testing, and executing exploits. It enables security professionals to simulate real-world attacks and identify vulnerabilities before malicious actors can exploit them.
A large database of payloads, auxiliary modules, and exploits is part of the system.. It also supports post-exploitation tasks such as privilege escalation and maintaining access. Metasploit is highly valuable for ethical hackers, red teams, and cybersecurity learners aiming to understand attack methodologies.
Top Features:
- Extensive library of exploits and payloads
- Post-exploitation and privilege escalation tools
- Integration with vulnerability scanners
- Automated penetration testing workflows
- Strong community and regular updates
4. Snort
Website:https://www.snort.org/
Snort is an open-source intrusion detection and prevention system (IDS/IPS) designed to monitor network traffic and detect malicious activities. It uses a rule-based language to analyze traffic in real time and generate alerts when suspicious behavior is detected.
Snort can function as a packet sniffer, packet logger, or full intrusion prevention system. It is widely used in enterprise environments to protect networks from attacks such as DDoS, port scans, and malware infections. Its flexibility and scalability make it a popular choice among security teams and is also recognized among open source cybersecurity tools.
Top Features:
- Real-time traffic analysis and packet logging
- Rule-based detection engine
- Intrusion detection and prevention capabilities
- Protocol analysis and content matching
- Highly customizable and scalable
5. OpenVAS
Website:https://www.openvas.org/
OpenVAS (Open Vulnerability Assessment System) is a comprehensive open-source vulnerability scanner used to identify security issues in systems and networks. It is part of the Greenbone Vulnerability Management suite and provides detailed reports on vulnerabilities.
The tool continuously updates its vulnerability database, ensuring accurate and up-to-date assessments. As part of Open Source Cybersecurity platforms, OpenVAS is particularly useful for organizations looking to maintain compliance and proactively fix security gaps. Its web-based interface makes it accessible for both technical and non-technical users.
Top Features:
- Comprehensive vulnerability scanning
- Regularly updated vulnerability database
- Detailed reporting and risk assessment
- Web-based user interface
- Supports authenticated and unauthenticated scans
6. Burp Suite Community Edition
Website:https://portswigger.net/burp/communitydownload
Burp Suite Community Edition is a widely used open source cybersecurity tools web application security testing tool designed for identifying vulnerabilities in web apps. It acts as an intercepting proxy, allowing users to inspect, modify, and analyze HTTP/HTTPS traffic between the browser and server.
Although the community version has limited automation compared to the professional edition, it still provides powerful manual testing capabilities. Security testers use it to detect issues like SQL injection, cross-site scripting (XSS), and authentication flaws. Its intuitive interface and modular design make it a favorite among beginners and professionals alike.
Top Features:
- Intercept and modify HTTP/HTTPS requests
- Web vulnerability scanning (manual)
- Spider tool for mapping applications
- Repeater and Intruder tools for testing
- User-friendly interface for security testing
7. Nikto
Website: https://cirt.net/Nikto2
Nikto is an open-source web server scanner that performs comprehensive tests against web servers to identify vulnerabilities, outdated software, and security misconfigurations. It is commonly used during the reconnaissance phase of penetration testing.
The tool scans for thousands of known issues, including dangerous files, insecure server configurations, and outdated components. While it may generate a high number of false positives, Nikto is still highly valuable for quickly identifying potential weaknesses in web infrastructure.
Top Features:
- Scans for over 6,000 known vulnerabilities
- Detects outdated server software
- Checks for dangerous files and configurations
- Supports SSL and multiple ports
- Command-line-based for automation
8. Aircrack-ng
Website:https://www.aircrack-ng.org/
Aircrack-ng is a complete suite of tools used for assessing Wi-Fi network security. It focuses on monitoring, attacking, testing, and cracking wireless network protocols, especially WEP and WPA/WPA2 encryption.
This toolset is widely used by ethical hackers and security professionals to evaluate the strength of wireless security implementations. It includes packet sniffing, deauthentication attacks, and password cracking capabilities, making it a powerful solution among open source cybersecurity tools for wireless penetration testing.
Top Features:
- Wi-Fi packet capture and analysis
- WEP and WPA/WPA2 password cracking
- Deauthentication attack support
- Performance optimization for faster cracking
- Cross-platform compatibility
9. OSSEC

Website:https://www.ossec.net/
OSSEC (Open Source Security) is a host-based intrusion detection system (HIDS) that monitors and analyzes system activity for signs of security threats. It provides log analysis, file integrity checking, rootkit detection, and real-time alerting.
OSSEC is highly scalable and can be used in both small and large environments. It supports centralized management, making it easier to monitor multiple systems from a single dashboard. Its ability to detect suspicious behavior at the host level makes it a crucial layer in cybersecurity defense.
Top Features:
- Log analysis and monitoring
- File integrity checking
- Rootkit detection
- Real-time alerting system
- Centralized management for multiple systems
10. John the Ripper
Website:https://www.openwall.com/john/
John the Ripper is a popular open-source password cracking tool used to test the strength of passwords and identify weak authentication practices. It supports a wide range of encryption algorithms and hash types and is widely recognized among open source cybersecurity platforms.
The tool is highly customizable and supports multiple attack modes, including dictionary attacks, brute force attacks, and hybrid methods. It is commonly used by security professionals to audit password security and improve authentication systems.
Top Features:
- Supports multiple hash and encryption formats
- Dictionary and brute-force attack modes
- Highly customizable and extensible
- Cross-platform support
- Efficient performance optimization
11. Kali Linux
Website:https://www.kali.org/
Kali Linux is a potent open-source operating system created especially for ethical hacking and penetration testing. It comes pre-installed with hundreds of cybersecurity tools, making it a complete platform for security professionals.
The OS is widely used for tasks such as network analysis, vulnerability assessment, digital forensics, and reverse engineering. As one of the Open Source Cybersecurity Tools, its flexibility allows it to run on desktops, virtual machines, and even mobile devices. Kali Linux is often the first choice for anyone entering the cybersecurity field.
Top Features:
- Pre-installed with 600+ security tools
- Supports penetration testing and forensics
- Regular updates and active community
- Customizable and open-source environment
- Available for multiple platforms (VM, USB, ARM)
12. ClamAV
Website:https://www.clamav.net/
ClamAV is an open-source antivirus engine and one of the open-source cybersecurity tools that can identify malware, viruses, trojans, and other harmful threats. It is widely used on mail servers and Linux systems for scanning files and ensuring system security.
The tool provides a command-line scanner along with automatic database updates. It is lightweight yet effective, making it suitable for both individual users and enterprise environments. ClamAV is especially popular for securing email gateways and file servers.
Top Features:
- Detects viruses, malware, and trojans
- Regularly updated virus database
- Command-line interface for automation
- Email scanning capabilities
- Cross-platform support
13. Wazuh
Website:https://wazuh.com/
Threat detection, integrity monitoring, incident response, and compliance management are all offered by the open-source security monitoring platform Wazuh.It builds on OSSEC and extends its capabilities with advanced analytics and integrations.
The platform offers real-time visibility into security events across endpoints, containers, and cloud environments. Wazuh integrates with tools like Elasticsearch and Kibana for powerful visualization and analysis, making it ideal for modern security operations centers (SOCs).
Top Features:
- Real-time threat detection and response
- Log data analysis and monitoring
- File integrity monitoring
- Cloud and container security support
- Integration with ELK stack for visualization
14. Hydra
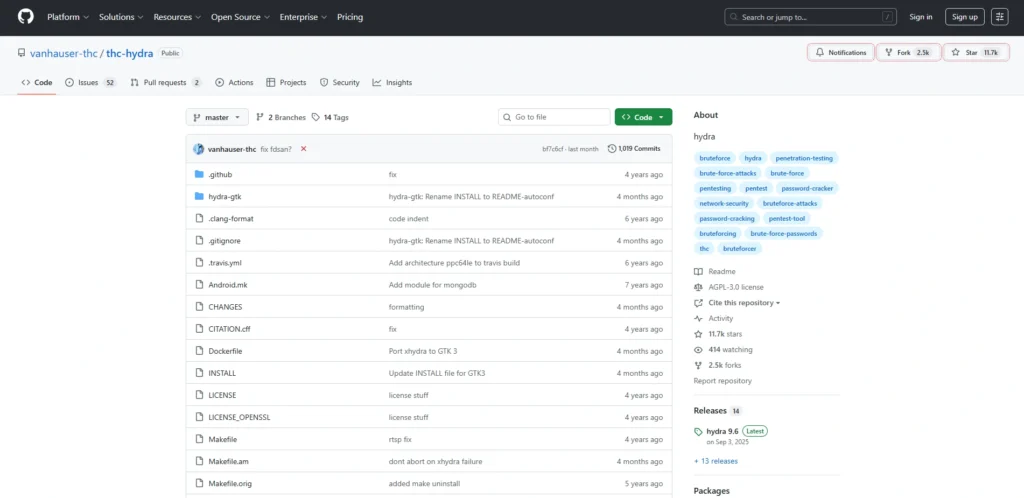
Website:https://github.com/vanhauser-thc/thc-hydra
Hydra (also known as THC Hydra) is a fast and flexible password-cracking tool used for brute-force attacks against various network services. It supports numerous protocols such as HTTP, FTP, SSH, and more.
Hydra is known for its speed and ability to perform parallelized attacks, making it highly efficient for testing login security. It is commonly used by penetration testers to identify weak credentials and improve authentication mechanisms, making it one of the open source cybersecurity tools.
Top Features:
- Supports multiple protocols (SSH, FTP, HTTP, etc.)
- Fast parallelized brute-force attacks
- Flexible and highly configurable
- Command-line-based for automation
- Lightweight and efficient
15. Security Onion
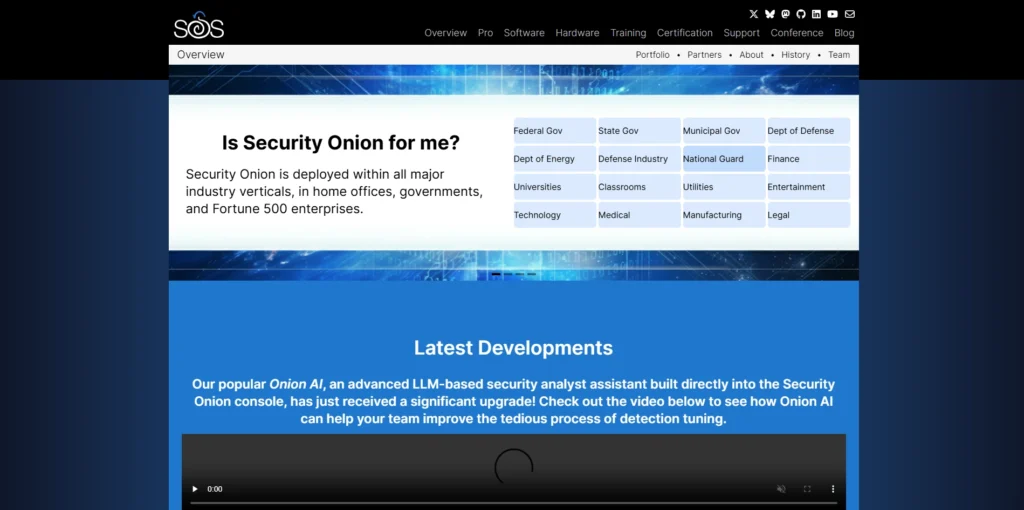
Website:https://securityonion.net/
Security Onion is a free and open-source platform for threat hunting, enterprise security monitoring, and log management. It combines multiple tools like Suricata, Zeek, and Elasticsearch into a unified solution.
The platform is designed for security analysts to detect and respond to threats in real time. It provides powerful dashboards, alerts, and deep packet inspection capabilities. Security Onion is widely used in SOC environments for network visibility and incident response.
Top Features:
- Integrated suite of Network monitoring tools
- Real-time threat detection and alerting
- Full packet capture and analysis
- Powerful dashboards and visualization
- Ideal for SOC and enterprise environments
Comparison Table
| Tool Name | Category | Best For | Key Feature | Platform |
| Wireshark | Network Analysis | Packet Inspection | Deep packet analysis | Windows/Linux/macOS |
| Nmap | Network Scanning | Port Scanning | Service & OS detection | Windows/Linux/macOS |
| Metasploit | Penetration Testing | Exploit Testing | Exploit framework | Windows/Linux/macOS |
| Snort | IDS/IPS | Network Security | Rule-based detection | Linux/Windows |
| OpenVAS | Vulnerability Scanner | Risk Assessment | Comprehensive scanning | Linux |
| Burp Suite Community | Web Security | Web Testing | Intercepting proxy | Windows/Linux/macOS |
| Nikto | Web Scanner | Server Scanning | 6000+ vulnerability checks | Linux/Windows |
| Aircrack-ng | Wireless Security | WiFi Testing | WPA/WEP cracking | Windows/Linux/macOS |
| OSSEC | HIDS | Log Monitoring | File integrity check | Linux/Windows/macOS |
| John the Ripper | Password Cracking | Password Testing | Multiple attack modes | Windows/Linux/macOS |
| Kali Linux | Security OS | All-in-one toolkit | 600+ tools | Linux |
| ClamAV | Antivirus | Malware Detection | Virus database updates | Windows/Linux/macOS |
| Wazuh | Security Monitoring | Threat Detection | SIEM integration | Linux |
| Hydra | Password Cracking | Brute Force Testing | Parallel attacks | Linux/Windows |
| Security Onion | Security Monitoring | SOC Operations | Full packet capture | Linux |
Conclusion
In conclusion, open source cybersecurity tools have made it much easier for anyone to improve their security without spending a lot of money. As a beginner, developer or a security professional, these tools provide you with the strength to observe networks, identify vulnerability and defend against system attacks.
The most rewarding aspect is that these tools are ever-evolving due to good community backing. The first tools that you can use are simple tools such as Wireshark or Nmap and then proceed to use more sophisticated tools such as Metasploit or Security Onion as you progress through. The appropriate mix of tools can enhance your overall cybersecurity strategy significantly and it is something that can be achieved by selecting the appropriate combination of tools depending on your needs.
FAQs
1. Are Open Source Security Tools Safe To Use?
Yes, most open source tools are safe and widely used by professionals. Since the code is open, it is regularly reviewed by the community, which helps in identifying and fixing vulnerabilities quickly.
2. Which Is The Best Open Source Cybersecurity Tool For Beginners?
Tools like Wireshark and Nmap are great for beginners because they are easy to learn and widely used for basic network analysis and scanning.
3. Can Open Source Tools Replace Paid Cybersecurity Software?
In many cases, yes. Open source tools offer powerful features that can match or even exceed paid tools. However, large enterprises may still prefer paid solutions for dedicated support and advanced integrations.
4. Do I Need Coding Skills To Use These Tools?
Not always. Some tools have user-friendly interfaces, but basic knowledge of networking and command-line usage can help you get better results.
5. How Do I Choose The Right Cybersecurity Tool?
You should choose tools based on your needs—such as network monitoring, vulnerability scanning, or penetration testing. It’s often best to use a combination of tools for complete security coverage.





